开发平台基本信息
芯片: 高通SM6225
版本: Android 13
kernel: msm-5.15
![[SM6225][Android13]user版本默认允许root和remount](https://www.ciyundata.com/zb_users/upload/2024/04/20240411183501171283170114100.jpeg)
问题描述
刚刚从Framework踏入性能的小殿堂,User版本默认是不会开启root权限的,而且一般调试需要设置一下CPU GPU DDR performance模式或者修改一些schedule util等调核调频节点去对比复测,userdebug版本的话本身整机性能就比user卡很多,有时候使用userdebug去复测会对测试结果有较大影响,与user测试结果存在很大差距。
基于以上,user+root闪亮登场,性能与user一致,而且还有root和remount权限,可以自主执行修改节点或者push等操作。话不多说,让我们进入整体,看看如何实现user+root+remount.
![[SM6225][Android13]user版本默认允许root和remount](https://www.ciyundata.com/zb_users/upload/2024/04/20240411183501171283170141395.jpeg)
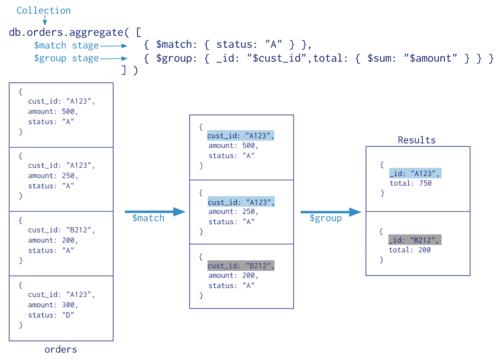
基线代码判断逻辑:
1.adb代码会检测相关属性
ro.secure
ro.debuggable (通过调用__android_log_is_debuggable()获取返回值)
2.代码path
2.1 adbd启动时检查属性,决定是否进行权限降级到AID_SHELL
path:system/adb/core/daemon/main.cpp line:121
if (should_drop_privileges()){
… …
2.2 system/adb/core/下搜索__android_log_is_debuggable()
3.修改思路
3.1 should_drop_privileges() 修改强制返回false,保持adb root用户级别
3.2 __android_log_is_debuggable() 返回true
packages/modules/adb/daemon/main.cpp
static bool should_drop_privileges() {
// The properties that affect `adb root` and `adb unroot` are ro.secure and
// ro.debuggable. In this context the names don't make the expected behavior
// particularly obvious.
//
// ro.debuggable:
// Allowed to become root, but not necessarily the default. Set to 1 on
// eng and userdebug builds.
//
// ro.secure:
// Drop privileges by default. Set to 1 on userdebug and user builds.
bool ro_secure = android::base::GetBoolProperty("ro.secure", true);
bool ro_debuggable = __android_log_is_debuggable();
// Drop privileges if ro.secure is set...
bool drop = ro_secure;
std::string build_prop = android::base::GetProperty("ro.build.type", "");
bool adb_build_root = (build_prop == "userdebug");
if (adb_build_root) {
return false;
}
// ... except "adb root" lets you keep privileges in a debuggable build.
std::string prop = android::base::GetProperty("service.adb.root", "");
bool adb_root = (prop == "1");
bool adb_unroot = (prop == "0");
if (ro_debuggable && adb_root) {
drop = false;
}
// ... and "adb unroot" lets you explicitly drop privileges.
if (adb_unroot) {
drop = true;
}
return drop;
}
解决方案:
1.注释掉DropCapabilitiesBoundingSet
说明:这个文件负责创建应用程序进程,并设置它们的权限和能力。需要注释掉DropCapabilitiesBoundingSet函数中的代码,以防止它删除adbd进程的任何能力。
文件路径:qssi/frameworks/base/core/jni/com_android_internal_os_Zygote.cpp
详细修改:
--- a/core/jni/com_android_internal_os_Zygote.cpp
+++ b/core/jni/com_android_internal_os_Zygote.cpp
@@ -681,7 +681,7 @@
}
static void DropCapabilitiesBoundingSet(fail_fn_t fail_fn) {
- for (int i = 0; prctl(PR_CAPBSET_READ, i, 0, 0, 0) >= 0; i++) {;
+ /*for (int i = 0; prctl(PR_CAPBSET_READ, i, 0, 0, 0) >= 0; i++) {;
if (prctl(PR_CAPBSET_DROP, i, 0, 0, 0) == -1) {
if (errno == EINVAL) {
ALOGE("prctl(PR_CAPBSET_DROP) failed with EINVAL. Please verify "
@@ -690,7 +690,7 @@
fail_fn(CREATE_ERROR("prctl(PR_CAPBSET_DROP, %d) failed: %s", i, strerror(errno)));
}
}
- }
+ }*/
}
static void SetInheritable(uint64_t inheritable, fail_fn_t fail_fn) {
2.启用abdb root模式添加remount,保持adb root用户级别
2.1 启用adbd进程的root模式,并添加remount到required中
说明:这个文件定义了adbd模块的编译选项和依赖项。需要添加-DALLOW_ADBD_ROOT=1到cflags中,以启用adbd进程的root模式,并添加remount到required中,以允许adbd进程重新挂载系统分区。
文件路径:qssi/packages/modules/adb/Android.bp
详细修改:
--- a/Android.bp
+++ b/Android.bp
@@ -50,6 +50,7 @@
"-Wvla",
"-DADB_HOST=1", // overridden by adbd_defaults
"-DANDROID_BASE_UNIQUE_FD_DISABLE_IMPLICIT_CONVERSION=1",
+ "-DALLOW_ADBD_ROOT=1",
],
cpp_std: "experimental",
@@ -112,7 +113,14 @@
name: "adbd_defaults",
defaults: ["adb_defaults"],
- cflags: ["-UADB_HOST", "-DADB_HOST=0"],
+ cflags: [
+ "-UADB_HOST",
+ "-DADB_HOST=0",
+ "-UALLOW_ADBD_ROOT",
+ "-DALLOW_ADBD_ROOT=1",
+ "-DALLOW_ADBD_DISABLE_VERITY",
+ "-DALLOW_ADBD_NO_AUTH",
+ ],
}
cc_defaults {
name: "host_adbd_supported",
host_supported: true,
target: {
linux: {
enabled: true,
host_ldlibs: [
@@ -606,6 +614,8 @@
"libcrypto_utils",
"libcutils_sockets",
// APEX dependencies.
"libadbd_auth",
"libadbd_fs",
"libcrypto",
"liblog",
],
+ required: ["remount",],
target: {
android: {
srcs: [
"daemon/abb_service.cpp",
"daemon/framebuffer_service.cpp",
"daemon/mdns.cpp",
"daemon/restart_service.cpp",
],
shared_libs: [
"libmdnssd",
2.2 保持adb root用户级别
说明:这个文件是adbd进程的主要入口点。我们需要修改should_drop_privileges函数,让它总是返回false,以防止它降低adbd进程的权限。should_drop_privileges() 修改强制返回false,保持adb root用户级别
文件路径:qssi/packages/modules/adb/daemon/main.cpp
详细修改:
--- a/daemon/main.cpp
+++ b/daemon/main.cpp
@@ -74,6 +74,7 @@
//
// ro.secure:
// Drop privileges by default. Set to 1 on userdebug and user builds.
+ return false;
bool ro_secure = android::base::GetBoolProperty("ro.secure", true);
bool ro_debuggable = __android_log_is_debuggable();
3.允许adbd进程关闭Verity检查,关闭selinux
3.1 允许adbd进程关闭Verity检查
说明:这个文件定义了fs_mgr模块的编译选项和依赖项。fs_mgr模块负责管理设备上的文件系统。我们需要修改-DALLOW_ADBD_DISABLE_VERITY=0为-DALLOW_ADBD_DISABLE_VERITY=1,以允许adbd进程关闭Verity检查。
文件路径:qssi/system/core/fs_mgr/Android.bp
详细修改:
--- a/fs_mgr/Android.bp
+++ b/fs_mgr/Android.bp
@@ -109,7 +109,8 @@
"libfstab",
],
cppflags: [
- "-DALLOW_ADBD_DISABLE_VERITY=0",
+ "-UALLOW_ADBD_DISABLE_VERITY",
+ "-DALLOW_ADBD_DISABLE_VERITY=1",
],
product_variables: {
debuggable: {
@@ -237,7 +238,8 @@
"fs_mgr_remount.cpp",
],
cppflags: [
- "-DALLOW_ADBD_DISABLE_VERITY=0",
+ "-UALLOW_ADBD_DISABLE_VERITY",
+ "-DALLOW_ADBD_DISABLE_VERITY=1",
],
product_variables: {
debuggable: {
3.2 允许init进程编译方式
说明:这个文件定义了init模块的编译选项和依赖项。init模块是设备启动时运行的第一个进程,负责初始化系统服务和属性。
-DALLOW_FIRST_STAGE_CONSOLE=1:允许init进程在第一阶段打开控制台输出
-DALLOW_LOCAL_PROP_OVERRIDE=1:允许init进程覆盖本地属性
-DALLOW_PERMISSIVE_SELINUX=1:允许init进程设置SELinux为permissive模式
-DREBOOT_BOOTLOADER_ON_PANIC=1:允许init进程在发生内核崩溃时重启到bootloader模式
-DWORLD_WRITABLE_KMSG=1:允许init进程设置kmsg文件为可写
-DDUMP_ON_UMOUNT_FAILURE=1:允许init进程在卸载分区失败时生成内存转储
-DSHUTDOWN_ZERO_TIMEOUT=1:允许init进程在收到关机命令时立即执行
文件路径:qssi/system/core/init/Android.bp
详细修改:
--- a/init/Android.bp
+++ b/init/Android.bp
@@ -136,13 +136,20 @@
"-Wno-unused-parameter",
"-Werror",
"-Wthread-safety",
- "-DALLOW_FIRST_STAGE_CONSOLE=0",
- "-DALLOW_LOCAL_PROP_OVERRIDE=0",
- "-DALLOW_PERMISSIVE_SELINUX=0",
- "-DREBOOT_BOOTLOADER_ON_PANIC=0",
- "-DWORLD_WRITABLE_KMSG=0",
- "-DDUMP_ON_UMOUNT_FAILURE=0",
- "-DSHUTDOWN_ZERO_TIMEOUT=0",
+ "-UALLOW_FIRST_STAGE_CONSOLE",
+ "-DALLOW_FIRST_STAGE_CONSOLE=1",
+ "-UALLOW_LOCAL_PROP_OVERRIDE",
+ "-DALLOW_LOCAL_PROP_OVERRIDE=1",
+ "-UALLOW_PERMISSIVE_SELINUX",
+ "-DALLOW_PERMISSIVE_SELINUX=1",
+ "-UREBOOT_BOOTLOADER_ON_PANIC",
+ "-DREBOOT_BOOTLOADER_ON_PANIC=1",
+ "-UWORLD_WRITABLE_KMSG",
+ "-DWORLD_WRITABLE_KMSG=1",
+ "-UDUMP_ON_UMOUNT_FAILURE",
+ "-DDUMP_ON_UMOUNT_FAILURE=1",
+ "-USHUTDOWN_ZERO_TIMEOUT",
+ "-DSHUTDOWN_ZERO_TIMEOUT=1",
"-DINIT_FULL_SOURCES",
"-DINSTALL_DEBUG_POLICY_TO_SYSTEM_EXT=0",
],
@@ -394,13 +401,20 @@
"-Wextra",
"-Wno-unused-parameter",
"-Werror",
- "-DALLOW_FIRST_STAGE_CONSOLE=0",
- "-DALLOW_LOCAL_PROP_OVERRIDE=0",
- "-DALLOW_PERMISSIVE_SELINUX=0",
- "-DREBOOT_BOOTLOADER_ON_PANIC=0",
- "-DWORLD_WRITABLE_KMSG=0",
- "-DDUMP_ON_UMOUNT_FAILURE=0",
- "-DSHUTDOWN_ZERO_TIMEOUT=0",
+ "-UALLOW_FIRST_STAGE_CONSOLE",
+ "-DALLOW_FIRST_STAGE_CONSOLE=1",
+ "-UALLOW_LOCAL_PROP_OVERRIDE",
+ "-DALLOW_LOCAL_PROP_OVERRIDE=1",
+ "-UALLOW_PERMISSIVE_SELINUX",
+ "-DALLOW_PERMISSIVE_SELINUX=1",
+ "-UREBOOT_BOOTLOADER_ON_PANIC",
+ "-DREBOOT_BOOTLOADER_ON_PANIC=1",
+ "-UWORLD_WRITABLE_KMSG",
+ "-DWORLD_WRITABLE_KMSG=1",
+ "-UDUMP_ON_UMOUNT_FAILURE",
+ "-DDUMP_ON_UMOUNT_FAILURE=1",
+ "-USHUTDOWN_ZERO_TIMEOUT",
+ "-DSHUTDOWN_ZERO_TIMEOUT=1",
"-DLOG_UEVENTS=0",
"-DSEPOLICY_VERSION=30", // TODO(jiyong): externalize the version number
],
3.3 关闭selinux 将enforce置为Permissive
说明:这个文件实现了一些与SELinux相关的函数。我们需要修改IsEnforcing函数,让它总是返回false,以防止它检查系统属性或内核参数是否设置了SELinux的强制执行。
文件路径:qssi/system/core/init/selinux.cpp
详细修改:
--- a/init/selinux.cpp
+++ b/init/selinux.cpp
@@ -123,6 +123,7 @@
}
bool IsEnforcing() {
+ return false;
// close selinux for user version with root
#if defined(LCT_BUILD_TYPE_FACTORY)
return false;
4.user 版本不允许 permissive domains
说明:user 版本启用 overlayfs 来装载 remount 对应分区 user 版本不允许 permissive domains
文件路径:system/sepolicy/Android.mk
详细修改:
--- a/Android.mk +++ b/Android.mk @@ -613,7 +613,7 @@ ifneq ($(filter address,$(SANITIZE_TARGET)),) local_fc_files += $(wildcard $(addsuffix /file_contexts_asan, $(PLAT_PRIVATE_POLICY))) endif -ifneq (,$(filter userdebug eng,$(TARGET_BUILD_VARIANT))) +ifneq (,$(filter user userdebug eng,$(TARGET_BUILD_VARIANT))) local_fc_files += $(wildcard $(addsuffix /file_contexts_overlayfs, $(PLAT_PRIVATE_POLICY))) endif
5.打开 USB 调试时默认授权,默认user版本编译remount。
5.1 默认开启usb调试
说明:默认开启usb调试。
文件路径:build/make//core/main.mk
详细修改:
--- a/core/main.mk
+++ b/core/main.mk
@@ -365,11 +365,11 @@
tags_to_install :=
ifneq (,$(user_variant))
# Target is secure in user builds.
- ADDITIONAL_SYSTEM_PROPERTIES += ro.secure=1
+ ADDITIONAL_SYSTEM_PROPERTIES += ro.secure=0
ADDITIONAL_SYSTEM_PROPERTIES += security.perf_harden=1
ifeq ($(user_variant),user)
- ADDITIONAL_SYSTEM_PROPERTIES += ro.adb.secure=1
+ ADDITIONAL_SYSTEM_PROPERTIES += ro.adb.secure=0
endif
ifeq ($(user_variant),userdebug)
@@ -377,7 +377,7 @@
tags_to_install += debug
else
# Disable debugging in plain user builds.
- enable_target_debugging :=
+ enable_target_debugging := true
endif
# Disallow mock locations by default for user builds
@@ -399,7 +399,7 @@
ADDITIONAL_SYSTEM_PROPERTIES += dalvik.vm.lockprof.threshold=500
else # !enable_target_debugging
# Target is less debuggable and adbd is off by default
- ADDITIONAL_SYSTEM_PROPERTIES += ro.debuggable=0
+ ADDITIONAL_SYSTEM_PROPERTIES += ro.debuggable=1
endif # !enable_target_debugging
## eng ##
5.2 添加remount
说明:user版本默认不会编译remount,即system/bin/remount不存在,需要将remount添加到默认编译列表里面。
文件路径:build/make/target/product/base_system.mk
详细修改:
--- a/target/product/base_system.mk
+++ b/target/product/base_system.mk
@@ -287,6 +287,7 @@
wificond \
wifi.rc \
wm \
+ remount \
ifneq ($(TARGET_HAS_LOW_RAM), true)
PRODUCT_PACKAGES += \
@@ -388,7 +389,6 @@
procrank \
profcollectd \
profcollectctl \
- remount \
servicedispatcher \
showmap \
sqlite3 \
总结
通过以上的修改,我们可以在Android 13上实现root功能。
希望这篇博客能对你有所帮助,如果你有任何问题或建议,欢迎留言讨论。谢谢!